Enterprise Access Model (EAM)
The Enterprise Access Model (EAM) represents a significant evolution in privileged access security, expanding beyond the traditional Active Directory Tier Model to address the complexities of modern hybrid and multi-cloud environments. While EAM provides a comprehensive framework for today's distributed enterprise landscape, it's crucial to understand that the AD Tier Model remains not just relevant, but mandatory for on-premises and hybrid infrastructures.
Evolution from the Legacy AD Tier Model
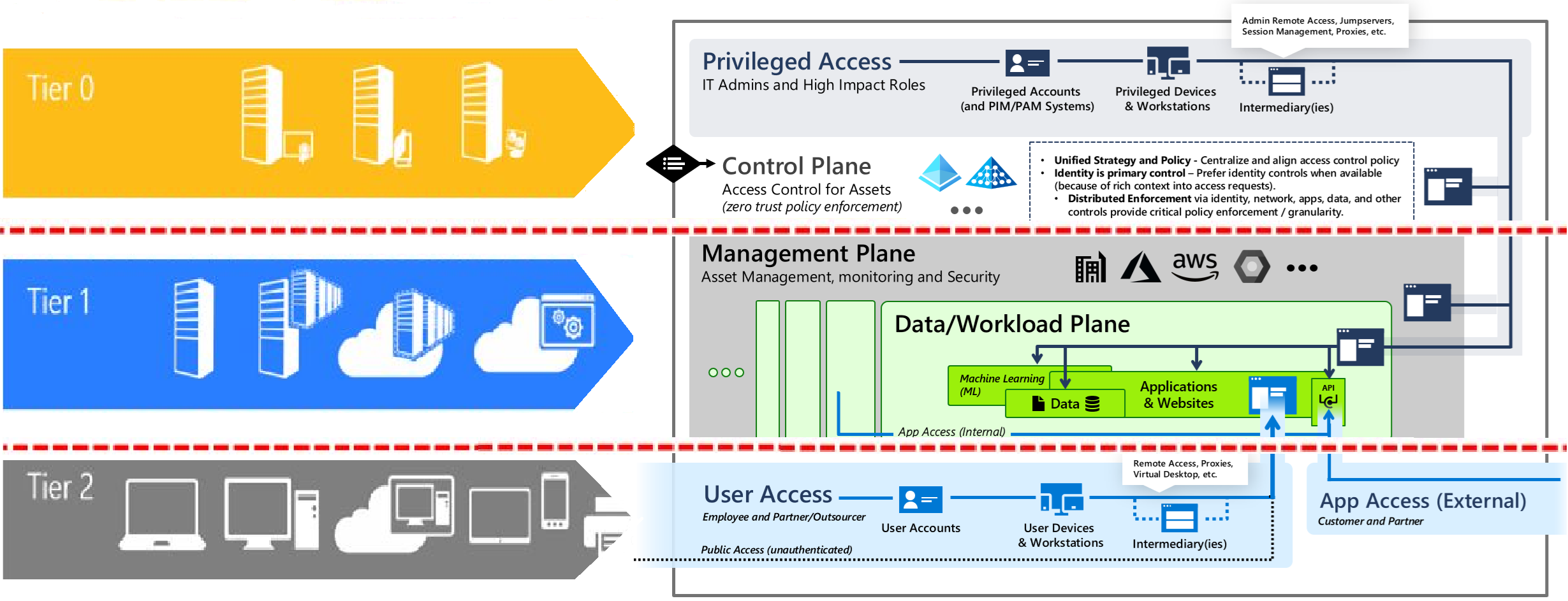
The legacy AD Tier Model was specifically designed to contain unauthorized privilege escalation within on-premises Active Directory environments. This proven three-tier architecture (Tier 0 for domain controllers and critical identity infrastructure, Tier 1 for server management, and Tier 2 for user workstations) established strict administrative boundaries that prevented credential theft and lateral movement within the AD forest.
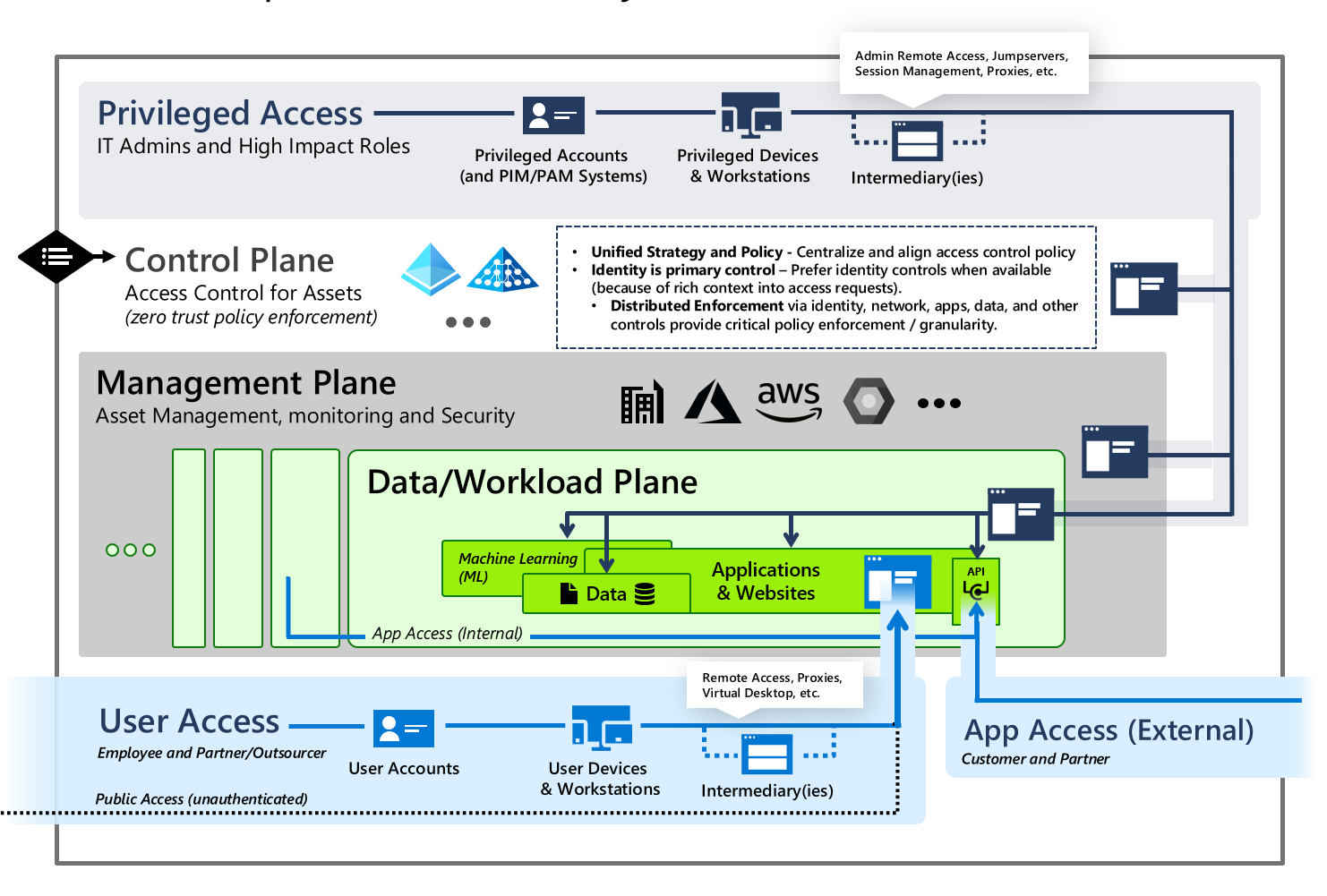
The Enterprise Access Model supersedes and extends this foundation by incorporating modern requirements such as cloud services, external user access, API pathways, and DevOps workflows. Rather than replacing the AD Tier Model, EAM expands its scope through a five-plane architecture: Control Plane (encompassing the original Tier 0), Management Plane, Data/Workload Plane, User Access, and App Access. This evolution addresses the reality that enterprises now operate across on-premises datacenters, Azure, AWS, and other cloud platforms simultaneously.
Critical Implementation Guidance
Here's the essential point that organizations must understand: If your environment includes on-premises Active Directory infrastructure—whether standalone or in a hybrid configuration with cloud services—you MUST implement and maintain the AD Tier Model. The EAM does not eliminate this requirement; it builds upon it.
For hybrid environments, the strategy becomes layered. Within your on-premises AD domain, strict tier-based segmentation remains non-negotiable. Domain controllers, privileged accounts, and administrative workstations must adhere to Tier 0 controls. Simultaneously, you extend protection into cloud resources using EAM's expanded planes, implementing Privileged Access Workstations (PAWs), Just-In-Time (JIT) access through Entra ID Privileged Identity Management, conditional access policies, and continuous monitoring.
The rationale is straightforward: on-premises Active Directory remains a primary target for attackers. Compromising a domain controller or Domain Admin account can cascade across your entire hybrid infrastructure, including Azure resources through federation and synchronization mechanisms. The AD Tier Model provides the foundational containment strategy that prevents this catastrophic scenario.
Organizations transitioning to cloud-native architectures without on-premises AD dependencies can focus solely on implementing the EAM framework with its Zero Trust principles and cloud-native controls. However, for the majority of enterprises maintaining hybrid infrastructures—which will remain the dominant deployment model for years to come—the AD Tier Model is not legacy; it's the essential foundation upon which modern privileged access security is built.
Privileged Access Workstations (PAWs): The Technical Safeguard
Privileged Access Workstations are hardened, dedicated systems that serve as secure administrative platforms, forming a critical component of both the AD Tier Model and EAM implementations. PAWs function as a security boundary between privileged credentials and potentially compromised endpoints, preventing credential harvesting attacks that exploit memory-resident credentials on multi-purpose systems.
The technical implementation of PAWs includes several key controls: application allowlisting that permits only approved administrative tools, restricted internet access preventing phishing and drive-by downloads, enforced multi-factor authentication at every logon, device attestation through TPM-backed certificates, and strict Group Policy configurations that disable credential caching. For Tier 0 operations, PAWs must never be used for email, web browsing, or any productivity tasks that could introduce malware vectors. This air-gap approach ensures that even if an administrator's regular workstation is compromised, attackers cannot pivot to privileged infrastructure.
In hybrid environments, PAWs must enforce context-aware access controls that verify device compliance state, network location, and authentication strength before permitting connections to both on-premises domain controllers and cloud management portals like Azure Portal or Microsoft 365 admin centers. Modern PAW implementations leverage Windows Defender Application Control (WDAC), Credential Guard, and Remote Credential Guard to provide defense-in-depth against sophisticated credential theft techniques.
High-Risk Roles and Catastrophic Impact Scenarios
Certain administrative roles possess capabilities that, in the hands of an attacker or malicious insider, can inflict catastrophic and potentially irrecoverable damage to an organization. Understanding these roles and implementing appropriate controls is paramount to enterprise security.
Domain Administrators and Enterprise Administrators represent the highest risk tier. Compromise of these accounts enables attackers to create persistent backdoors through Golden Ticket attacks (forging Kerberos TGTs), modify GPOs to deploy ransomware enterprise-wide, exfiltrate entire AD databases containing password hashes, disable security controls and logging, or establish skeleton keys that bypass authentication. The material impact includes complete operational shutdown, regulatory compliance violations with associated fines, intellectual property theft, and reputational damage that can permanently affect customer trust and stock valuations.
Backup Administrators and Storage Administrators control an organization's recovery capabilities. Malicious actors with these privileges can delete or encrypt backup repositories, rendering ransomware attacks unrecoverable and forcing organizations to pay extortion demands. Modern ransomware operators specifically target backup infrastructure—including cloud-based backup services—before deploying encryption payloads. Without properly secured backup admin accounts through tier segmentation and PAW enforcement, organizations lose their last line of defense against data loss.
PKI Administrators and Certificate Authority operators can issue fraudulent certificates for code signing (enabling malware deployment that bypasses security controls), SSL/TLS interception (man-in-the-middle attacks on encrypted communications), or authentication certificates (impersonating any user or service). Compromised PKI infrastructure requires complete rebuild and re-issuance of all certificates—a process that can take months and disrupt every digital service.
Cloud Global Administrators (Azure/Microsoft 365) can modify conditional access policies to create backdoor access, export all organizational data including emails and OneDrive contents, delete cloud resources including production databases and virtual machines, or modify federation settings to persist access even after password resets. In hybrid environments without proper tier separation, compromising a cloud Global Administrator can provide pathways to on-premises infrastructure through Azure AD Connect or Entra Cloud Sync servers.
How the Models Address These Threats
The AD Tier Model and EAM address these risks through enforcement of the no-credential-crossing principle. Tier 0 credentials never authenticate to lower-tier systems where malware might capture them. Authentication Policy Silos in Windows Server restrict where privileged accounts can logon, technically enforcing tier boundaries through Kerberos ticket issuance controls. Protected Users security group membership prevents credential caching and forces modern authentication protocols.
Just-In-Time (JIT) access, a core EAM component, limits the temporal window of exposure. Instead of permanent Domain Admin membership, administrators request time-bound elevation through Entra ID Privileged Identity Management, reducing the attack surface to hours instead of perpetual risk. Combined with audit logging, JIT access creates forensic evidence trails that detect anomalous privilege usage patterns.
For hybrid infrastructures specifically, the models require separate administrative accounts for on-premises (AD Tier 0) and cloud (EAM Control Plane) operations, preventing single-credential compromise from cascading across the entire environment. This separation, enforced through PAWs with network isolation and conditional access policies verifying device compliance, creates multiple independent security boundaries that attackers must breach sequentially—dramatically increasing detection likelihood and defensive response time.